Digital Forensic Investigation Methods and Tools Used by Law Enforcement
Digital forensics is a scientific process used to collect, preserve, analyze, and present digital evidence from electronic devices. Law enforcement agencies and cybercrime investigators rely on digital forensic techniques to investigate crimes involving mobile phones, computers, networks, and cloud platforms.
Digital forensics is a scientific process used to collect, preserve, analyze, and present digital evidence from electronic devices. Law enforcement agencies and cybercrime investigators rely on digital forensic techniques to investigate crimes involving mobile phones, computers, networks, and cloud platforms.
Digital evidence must be handled carefully so that it remains legally admissible in court. For this reason, investigators follow strict forensic procedures and use specialized forensic tools.
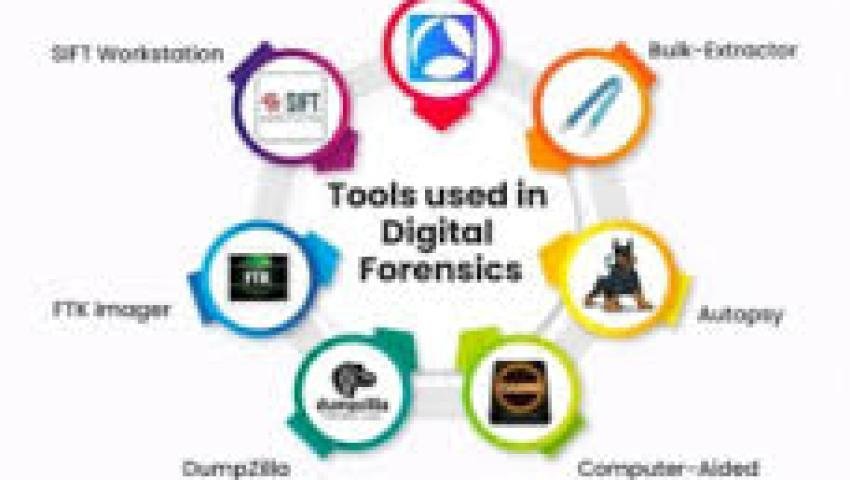
Below are the major digital forensic investigation methods and tools used by investigators worldwide.
1. Data Acquisition (Evidence Collection)
The first step in digital forensic investigation is data acquisition. Investigators create a forensic copy (image) of a device or storage media without altering the original data.
This process ensures that the original evidence remains untouched.
Common Data Acquisition Methods
Disk Imaging – Creating a complete copy of a hard drive or storage device
Logical Acquisition – Extracting accessible files from the system
Physical Acquisition – Capturing the entire storage including deleted data
Live Acquisition – Collecting data from a running system
Popular Data Acquisition Tools
FTK Imager
EnCase Forensic Imager
Guymager
Magnet Acquire
dd (Linux forensic imaging tool)
These tools generate forensic images that investigators analyze later.
2. Mobile Device Forensics
Mobile phones contain a huge amount of digital evidence such as messages, call logs, photos, location history, and app data.
Mobile forensic tools are used to extract data from smartphones without damaging the device.
Data Extracted from Mobile Devices
Investigators can recover:
Call history
SMS and MMS messages
WhatsApp chats
Deleted files
Photos and videos
App data
Location history
Popular Mobile Forensic Tools
Cellebrite UFED
MSAB XRY
Oxygen Forensic Detective
Magnet AXIOM
Elcomsoft iOS Forensic Toolkit
These tools support both Android and iOS devices.
3. Computer and Hard Disk Forensics
In many cybercrime cases, computers and laptops contain crucial evidence.
Investigators analyze storage devices to identify:
Deleted files
Hidden data
Malware artifacts
Internet browsing history
File access logs
Common Computer Forensic Tools
EnCase Forensic
FTK (Forensic Toolkit)
Autopsy Digital Forensics Platform
Sleuth Kit
X-Ways Forensics
These tools allow investigators to examine disk images and recover hidden or deleted information.
4. Network Forensics
Network forensics focuses on analyzing network traffic and logs to identify suspicious activity.
It is commonly used in cases involving:
hacking attacks
malware infections
data breaches
insider threats
Network Forensic Investigation Methods
Investigators analyze:
network packets
firewall logs
server logs
DNS records
IP addresses
Popular Network Forensic Tools
Wireshark
NetworkMiner
tcpdump
Security Onion
Zeek (formerly Bro)
These tools help investigators identify attack patterns and malicious communication.
5. Memory Forensics (RAM Analysis)
Sometimes attackers use techniques that leave traces only in system memory (RAM) rather than on disk.
Memory forensics helps investigators analyze running processes and detect hidden malware.
Information Extracted from RAM
Investigators can identify:
running processes
encryption keys
malware artifacts
network connections
command history
Memory Forensic Tools
Volatility Framework
Rekall
Belkasoft RAM Capturer
Magnet RAM Capture
This technique is especially useful in advanced cybercrime investigations.
6. Email Forensics
Email is often used in cybercrime activities such as phishing, fraud, and corporate espionage.
Email forensic analysis helps investigators trace:
sender information
email headers
IP addresses
server routes
Email Forensic Tools
MailXaminer
Aid4Mail
Paraben Email Examiner
Autopsy Email Analysis
Investigators also analyze email headers to identify the original sender and email server path.
7. Cloud Forensics
Modern cybercrime investigations often involve cloud platforms such as Google Drive, Dropbox, AWS, and Microsoft Azure.
Cloud forensic investigation focuses on:
cloud storage data
access logs
authentication records
account activity history
Cloud Forensic Tools
Magnet AXIOM Cloud
Elcomsoft Cloud Explorer
Oxygen Cloud Extractor
AWS CloudTrail analysis tools
These tools help investigators analyze data stored in cloud services.
8. Malware Forensics
Malware analysis is important in cases involving ransomware, spyware, and hacking attacks.
Investigators analyze malicious software to understand:
how the malware works
what data it steals
how it spreads across systems
Malware Analysis Tools
IDA Pro
Ghidra
Cuckoo Sandbox
Any.Run
REMnux
These tools help reverse engineer malware and identify attack techniques.
Digital Forensic Investigation Process
A standard digital forensic investigation usually follows these steps:
Identification – Finding potential digital evidence
Preservation – Protecting evidence from alteration
Collection – Creating forensic copies of data
Analysis – Examining the data using forensic tools
Documentation – Recording investigation findings
Presentation – Presenting evidence in court
Following this structured process ensures that digital evidence remains legally valid and reliable.
Conclusion
Digital forensics plays a critical role in modern investigations. By using specialized forensic tools and scientific methods, investigators can uncover hidden digital evidence from mobile devices, computers, networks, and cloud systems.
As cybercrime continues to grow, digital forensic investigation will remain one of the most important tools for law enforcement agencies, cybercrime investigators, and security professionals.
Mrityunjay Singh
Leave a comment
Your email address will not be published. Required fields are marked *

